As you navigate the ever-changing digital landscape, protecting your online privacy and security is now more crucial than ever before in the Linux operating system. Fortunately, some Linux distributions offer an additional layer of security, making them a popular choice for privacy-conscious users like yourself.
While several open-source Linux distributions are available, the best security-focused Linux distributions can protect you from cybersecurity threats such as phishing, criminal attacks, and government monitoring.
Throughout this article, we will introduce you to privacy and security in the context of Linux distributions and emphasize the significance of online security. This article will also examine the unique features of security-focused Linux distributions and offer practical tips and tricks for using them.
Importance Of Security and Privacy
Privacy and security in the digital realm have a close relationship. However, the concepts are quite distinct. Understanding the concepts beforehand is vital to choosing a Linux distro with the best privacy and security capabilities.
Privacy refers to the right of individuals to control their personal information and to be free from unwarranted intrusion into their private lives. It protects personal data such as names, addresses, financial information, and online activities from unauthorized access, use, and disclosure. It is important because individuals share more personal information online and through digital devices.
Security, conversely, refers to protecting systems, networks, and data from unauthorized access, use, and modification. It involves implementing encryption, firewalls, and access controls to prevent and mitigate security threats like malware, hacking, and cyberattacks. Security is essential for protecting personal data and other sensitive information from theft, unauthorized access, and misuse.
Privacy and Security are essential components of digital safety. They are necessary to ensure that individuals can exercise their rights to privacy and free speech in a secure and protected environment. They also play a crucial role in protecting individuals, businesses, and organizations from unauthorized access, theft, and misuse of sensitive and personal information.
Besides, they help prevent identity theft, fraud, and cybercrime and safeguard confidential data such as financial information, health records, and intellectual property.
Most Secure Linux Distributions for Privacy
The following are the best privacy and security-focused Linux distributions to consider:
1. Qubes OS
Qubes OS is a security-focused operating system first released in 2012 by developer Joanna Rutkowska and her team at the Invisible Things Lab. It provides isolation between different applications and activities to minimize the impact of any security vulnerabilities that attackers might exploit.
Qubes OS uses a unique approach to security called “security by compartmentalization“. This means that it divides the different applications and activities on the system into separate virtual machines (domains), with each one running in its isolated environment. This makes it more difficult for an attacker to gain access to sensitive information or compromise the system.
It uses a package management system based on the Fedora distribution, allowing users to install and update software easily. It also supports using “AppVMs,” lightweight virtual machines designed to run specific applications. This feature allows users to compartmentalize their activities further and reduce the risk of cross-contamination between different activities.
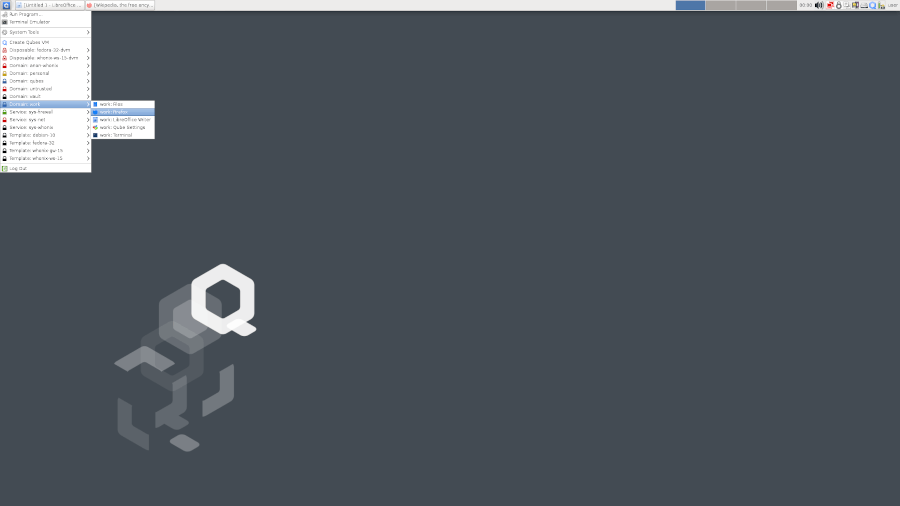
Why Qubes OS? Well, Qubes OS is a good choice for users concerned about security and who want a system designed with that in mind. Its domains provide an added layer of protection against various threats, and its package management system makes it easy to keep software up-to-date.
2. Kali Linux
Kali Linux is a Debian-based Linux distribution designed for digital forensics, penetration testing, and security auditing. It is the work of Mati Aharoni and Devon Kearns of Offensive Security and was released in 2013 for the first time as a successor to BackTrack Linux.
Kali Linux uses the Advanced Package Tool (APT) as its software management system, which allows users to install and update software packages quickly. It comes with a wide range of security tools pre-installed, including tools for network analysis, vulnerability scanning, password cracking, and exploitation.
Kali Linux receives regular updates to ensure its tools and packages are up-to-date and secure. The distribution also offers customizable installation options, allowing users to select only the tools and packages they need for their specific security needs.

Kali Linux is suitable for security professionals, researchers, and enthusiasts who want a powerful and flexible security testing and analysis platform. It may not be the best choice for general-purpose use, as its focus on security and penetration testing may limit compatibility with specific applications or devices.
However, it can be a valuable tool for cybersecurity professionals.
3. Whonix
Whonix is a free and open-source desktop operating system based on the Tor anonymity network and Debian GNU/Linux. It is designed to provide strong privacy and anonymity on the internet and dates back to 2012.
Whonix consists of two machines connected through an isolated network. One machine acts as the client or Whonix-Workstation, the other as a proxy. The first release under the name of Whonix happened with version 0.4.4, rebased on Debian.
It uses ATP, the popular Debian package management system. Users can install additional software using apt-get or Synaptic Package Manager. Whonix provides the best possible protocol for leak protection and fingerprinting protection. Java, JavaScript, Flash, browser plugins, and misconfigured applications cannot leak the user’s actual external IP address.
Interestingly, Whonix has several notable features such as security-focused Linux Distribution Kicksecure, Tor anonymity network, Debian GNU/Linux, and the principle of security by isolation.
Whonix is ideal for anyone who values privacy, has business secrets, needs private communication, or does not want to be tracked by advertisers or governments. It is also suitable for journalists, activists, whistleblowers, and anyone else.
4. Kodachi
Linux Kodachi is a security-focused distribution built for anonymity and privacy. It was developed by an anonymous person or group within the Kodachi team and released in 2016. The operating system can be run from a DVD or USB thumb drive and filters all network traffic through a VPN and the Tor network, obscuring the user’s network location.
When the operating system starts, it automatically changes the user’s MAC address and starts VPN and TOR network services. Then it forces all traffic through the VPN + TOR network tunnel with DNS encryption.
Kodachi has built-in anonymity, cryptography, and anti-forensic features not provided by other operating systems. It features a dashboard showing detailed security information about your current session and a long list of configuration options. The operating system also has a Torified Shell that allows users to run commands through Tor.

Kodachi OS is very friendly compared to its competitor operating systems and requires no prior knowledge. With preconfigured firewalls, Kodachi is easy to use. It takes an hour or less for anyone to learn how to use it. Besides, the distribution attempts to clean up by removing traces of its use from the computer.
Linux Kodachi is ideal for anyone looking for an extra layer of privacy on their desktop or laptop. It is especially suitable for those who value privacy but needs to learn Linux since it was designed specifically for them.
5. Tails
Tails or The Amnesic Incognito Live System is a Debian-based Linux distribution focusing on security and anonymity. You can boot it as a live DVD or live USB, and it will leave no trace of the user’s activities on the computer. Tails connect to the Internet exclusively through the anonymity network Tor, which helps preserve privacy and anonymity.
The system is not intended for everyday use but for security paranoids looking for maximum personal security and anonymity on the Internet.
Tails was first released in 2009 by a group of developers who wanted to create an operating system that would help people protect their privacy and avoid censorship. The project receives funding from individuals and organizations supporting its mission.
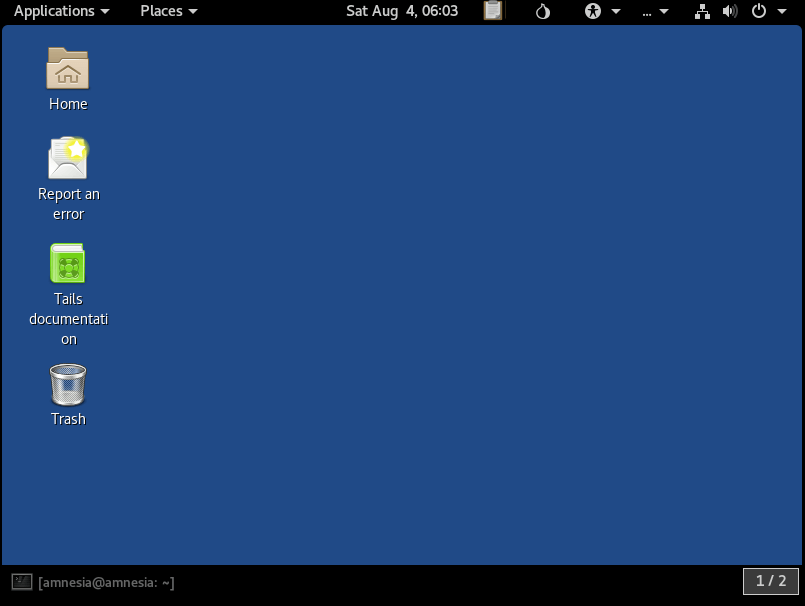
Tails uses Debian’s package management system to manage software updates. It also includes pre-installed software such as Tor Browser, Thunderbird email client with Enigmail encryption, LibreOffice suite, KeePassXC password manager, and more. The developers recently released Tails 5.4 with several improvements, such as hardening several aspects of the Linux kernel, updating Tor Browser to version 11.5.2, bumping up the Tor service to 0.4.7.10, and disabling HTTPS-only mode in the Unsafe Browser for user convenience, making it easier to connect to Wi-Fi networks.
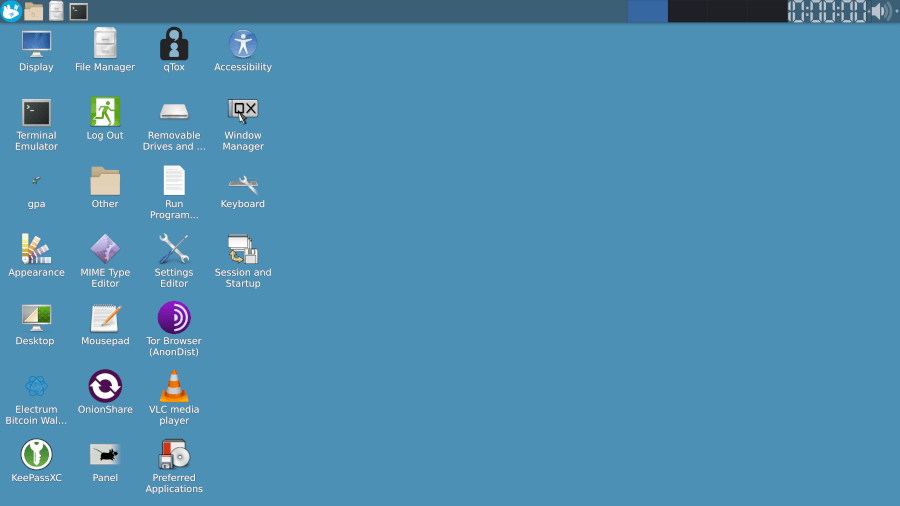
6. Parrot Security OS
Parrot Security OS is a free and open-source Linux distribution based on Debian, designed for security, privacy, and development. It was first publicly released on April 10th, 2013, by Lorenzo Faltra, the current team lead, core developer, infrastructure manager, and release manager.
Parrot Security OS follows a Linux rolling release development model with three editions: Home Edition, Security Edition, and Cloud Edition.
The Home Edition is ideal for daily users who need a “lightweight” system on their laptops or workstations. It includes programs to chat privately with people, encrypt documents, or browse the internet anonymously.
The Security Edition is ideal for penetration testing and forensic analysis. It comes with pre-installed tools for penetration testing, such as Metasploit Framework and Nmap.
On the other hand, the Cloud Edition offers several other noteworthy editions of Parrot Security built for cloud environments, virtual machines, embedded devices, and other special deployments. It also provides Docker images to enable users to leverage Parrot OS tools on top of other operating systems or in cloud environments.
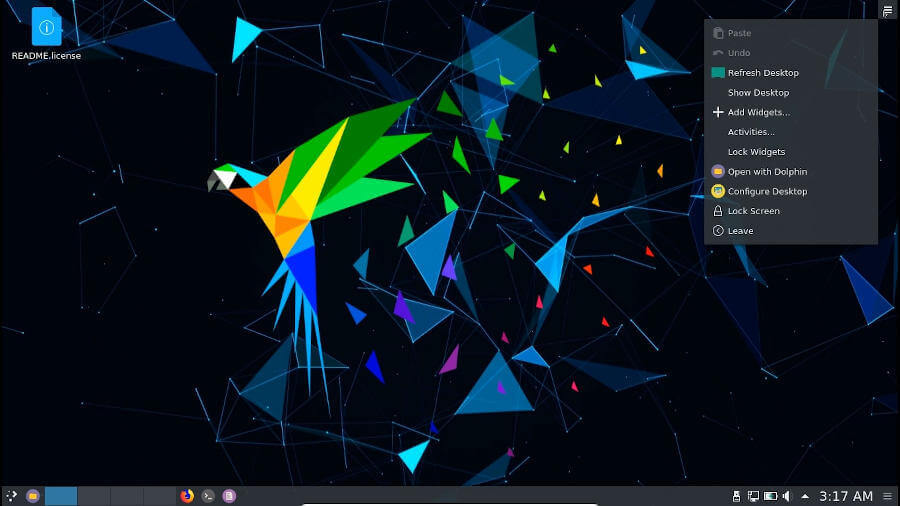
Parrot Security OS uses the APT package management system like most Debian-based distributions. Users can install additional software packages using the apt-get command-line tool or Synaptic Package Manager GUI tool.
Notable features of Parrot Security OS include the Tor network and Tor browser, which come pre-installed in the system. Onion Share is an open-source utility that you can use to share files of any size over the Tor network securely and anonymously.
Parrot Security OS is ideal for daily Linux users, software developers, system administrators, system programmers, and computer science/engineering students who need a secure environment to work in. It is also suitable for people into pen-testing who want an open-source operating system with pre-installed security tools.
7. BlackArch Linux
BlackArch Linux is a penetration testing distribution based on Arch Linux that provides many cybersecurity tools. It is an open-source distro first released in 2013 by BlackArch Linux volunteers. It uses Pacman as its package manager and can be installed as an unofficial user repository on any current Arch Linux installation.
BlackArch Linux has over 2000 security-related software tools arranged logically. Notable software tools include DoS (Denial of Service), backdoor, networking, and more. You can conveniently install all the tools simultaneously, in groups, or individually.
BlackArch only provides the Xfce desktop environment in the “Slim ISO” but provides multiple preconfigured Window Managers in the “Full ISO“.
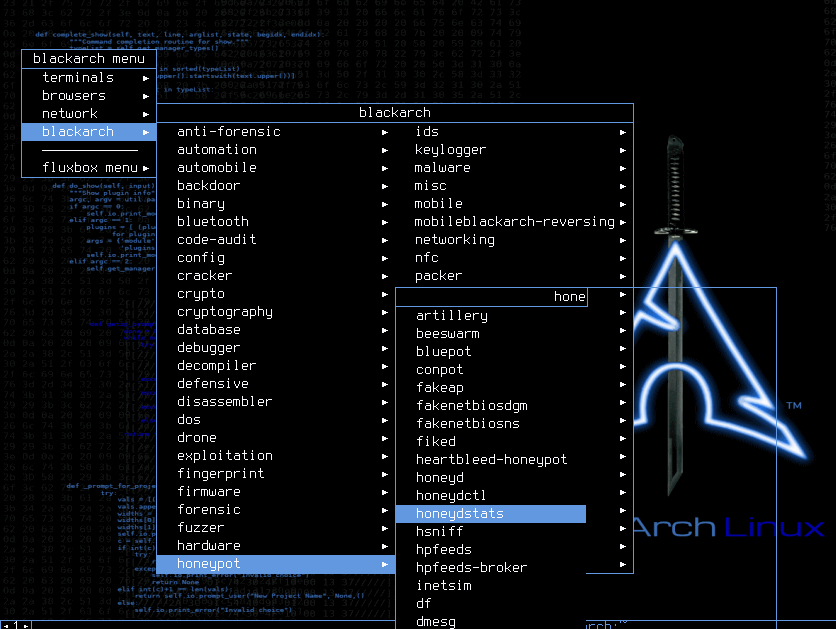
One notable feature of BlackArch Linux is its absence of a graphical user interface (GUI). This might make it less appealing to some users who prefer GUIs.
However, this feature makes it ideal for people interested in pen-testing and cybersecurity who want to set up their workstations just as they would without any unnecessary software. It is also suitable for Arch lovers who want to explore new ways of using Arch-based distros.
8. SELinux
Security-Enhanced Linux (SELinux) is a security module implemented in the Linux kernel to provide Mandatory Access Control (MAC) policies. It was released in 2000 by the United States National Security Agency (NSA) as an open-source software project.
SELinux enhances the Linux kernel’s security by providing fine-grained access control policies that restrict the actions that system processes and users can perform. It helps to protect against various security threats, including zero-day exploits, privilege escalation attacks, and malware infections.
SELinux works by labeling every object (such as files, directories, and network ports) and every process with a security context. Access control policies define the actions allowed or denied based on the security context of the object and process. This mechanism provides a powerful layer of protection that can be customized and tailored to meet the specific security needs of a system.
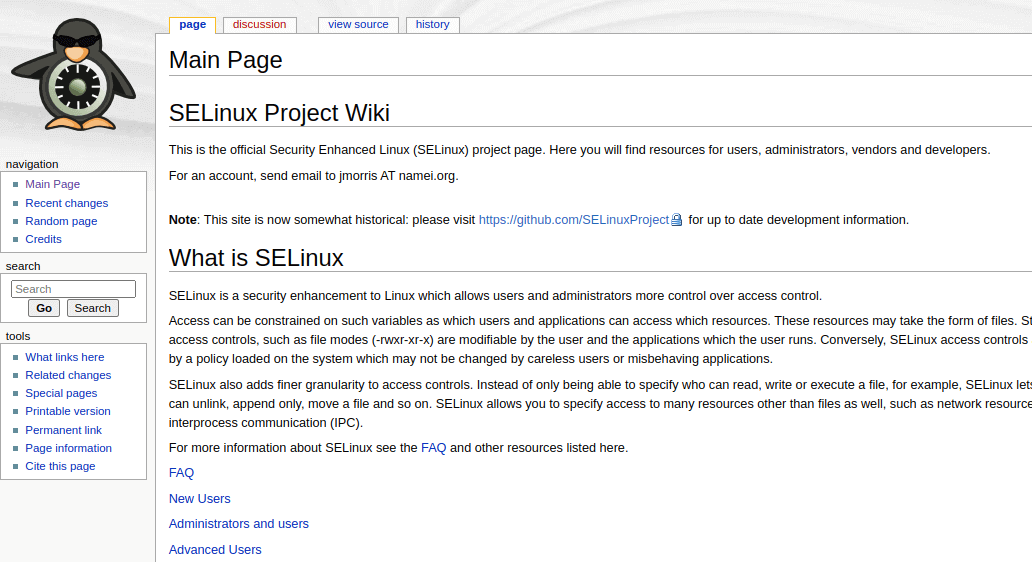
SELinux has built-in software management capabilities, and you can easily install it using a package manager like YUM or APT. Once installed, you can configure SELinux policies and manage them using various command-line tools or graphical user interfaces, such as the SELinux Management Console.
SELinux is ideal for organizations and individuals who require a high level of security for their Linux systems. This includes government agencies, financial institutions, healthcare providers, and other organizations that deal with sensitive data or information.
However, SELinux can be complex and requires expertise to set up and manage effectively, so it may not be suitable for less experienced users or small-scale deployments.
9. Discreete Linux
Discreete Linux is a security-focused operating system that Discreete Security Solutions developed. It was first released in 2021 and designed to provide high-level protection against cyber threats, particularly for users who require anonymity and privacy.
Discreete Linux includes various built-in security features, such as full disk encryption, network traffic encryption, and secure boot. It also uses the Tor network to provide anonymous internet browsing and communication. Additionally, it includes a range of privacy-focused applications, such as the Tor Browser, encrypted email clients, and password managers.
Formerly known as Ubuntu Privacy Remix, Discreete Linux is managed through its package manager and designed to ensure that all installed software is fully vetted for security issues. The operating system can be run as a live CD or installed onto a computer’s hard drive.
Discreete Linux is ideal for individuals or organizations requiring high security and privacy, such as journalists, activists, or researchers working on sensitive topics. However, due to its focus on security and privacy, it may not be suitable for users who require access to a wide range of mainstream applications or software.
10. Alpine Linux
Alpine Linux is a small, security-oriented, and lightweight Linux distribution designed for power users who appreciate security, simplicity, and resource efficiency. It was developed by the Alpine Linux development team and released in 2005.
The distribution uses musl libc, BusyBox utility platform instead of GNU, and OpenRC instead of the more commonly used systemd. These features make it small and very resource-efficient. A container requires no more than 8 MB, and a minimal installation to disk requires around 130 MB of storage.
It uses its own package manager called apk, the OpenRC init system, script-driven set-ups, and that’s it! This gives you a simple, crystal-clear Linux environment without all the noise. The distribution uses the apk package manager, which adds, deletes, and repairs packages.
One notable feature of Alpine Linux is its software management. Binary packages are thinned out and split, giving you even more control over what you install, and keeping your environment as small and efficient as possible. Other security features prevent stack buffer overflow and memory corruption for every package installed on the OS.
Alpine Linux is ideal for power users who appreciate security, simplicity, and resource efficiency. It is also suitable for routers, firewalls, VPNs, VoIP box containers, and servers. If you’re looking for a lightweight Linux distribution that aims for minimalism in terms of space and scope as well as higher security, then Alpine Linux might be an excellent choice.
Conclusion
In conclusion, Linux provides a range of security-focused distributions to meet the needs of various users. These distributions offer different features and tools to ensure systems and data security.
Whether you’re a security professional, a privacy-conscious user, or someone who needs a lightweight and secure operating system, there is a Linux distribution that can meet your requirements.
The top 10 best security-focused Linux distributions discussed above are among the most popular and widely used in the security community, and each offers unique benefits and advantages.
